This article includes updates for Certificate Manager 8.10.
This article describes how to create a new self-signed or secondary Certificate Authority (CA) to be used in Smart ID Certificate Manager (CM). This task is done in Administrator's workbench (AWB) in Certificate Manager (AWB).
Prerequisites
The following prerequisites apply:
-
Two administration officers must sign the request.
-
Both officers must have the following roles:
-
Use AWB
-
CA and Key tasks
-
-
A connection to the CM host must have been established. See Connect to a Certificate Manager host.
-
The following information is required by the officer during the task:
-
The CA name that will appear in the Authority Hierarchy in the explorer bar
-
The name of the issuing CA when creating subordinate CAs
-
CA key to be used for the certificate, see Create CA key in Certificate Manager
-
The signature algorithm
-
The distribution rules applicable
-
The applicable certificate format is generated
-
Step-by-step instruction
Request CA
Clicking Save at any time during the creation of the Authority, before clicking OK, will save the data and place the incomplete Authority request in the Authority Hierarchy.
To complete the creation of the Authority at a later stage:
-
Highlight the unsigned Authority in the explorer bar.
-
Select Modify from the Edit menu, the toolbar, or the right-click shortcut menu.
To create a CA request:
-
In AWB, select New > Authority.
-
In the Create Authority Request dialog, enter the Authority name that should appear in the Authority Hierarchy in the explorer bar. This field is mandatory.
-
Set the CA State to Active or Closed as required.
-
Select Domain and check Visible in subdomain if applicable.
-
Select the Authority type CA.
-
Modify Valid from and Expiration date by selecting the days, hours, and minutes, and adjust the values with the up and down arrows. The date and time units may also be entered manually.
If the CA is to be a subordinate CA, issued with a standard format definition, the expiration date will be truncated to the expiration date of the issuing CA if necessary.
-
If the CA is to be a self-signed (root) CA, keep Issuing CA - Self signed checked (default) and go to step 8.
-
If the CA is to be a subordinate CA, do the following:
-
Uncheck Issuing CA - Self signed. Issuing CA is enabled. This field is now mandatory.
-
Click the browse button, select the required CA and click OK.
The selected CA appears in Issuing CA.
-
-
Select the CA Usage by checking Certificate signing and/or CRL signing. Selection of at least one option is mandatory.
-
In Key, click the browse button, select the required key and click OK.
The selected key appears in the Key field. This field is mandatory. -
If an RSA key was selected, select a Key algorithm.
The key algorithm is used to restrict an RSA key to be used only for RSASSA-PSS signatures or only with the selected RSASSA-PSS parameters. The drop-down list contains only those algorithms that matches the specified algorithmOID for the CIS device that holds the selected key, see the device configuration in cis.conf. The selected algorithm will be set in the subjectPublicKeyInfo field in the issued CA certificate.
-
Select a Signature algorithm. The drop-down list contains only those algorithms that matches the key algorithm for the key for the selected issuing CA, that is, self-signed or the selected CA.
If the hashInCis property is set to true and a signAlgorithm or signMechanism is specified for the device that holds the selected CA key, see the device configuration in cis.conf. The selected signature algorithm must be the same as the algorithm specified for the device in cis.conf. No warning message is displayed if any other signature algorithm is selected.
-
If immediate publishing is wanted, do the following steps in Distribution rules, for each relevant distribution rule:
-
Click on + to open the Select Distribution Rules window.
-
Select the required distribution rule for the CA certificate from the list in the window and click OK.
-
-
When all the relevant distribution rules have been entered, edit the processing order of distribution rules if needed. To change the order, select a procedure and use the arrow buttons to move it up or down. The distribution rules will be processed in the order selected and then stored in CMDB.
-
In Format, click the browse button, select the required format and click OK.
The selected certificate format appears in the Format field. This field is mandatory.Once a format has been selected, you can customize the set of format definition fields and modules.
-
At Format, click Advanced.
-
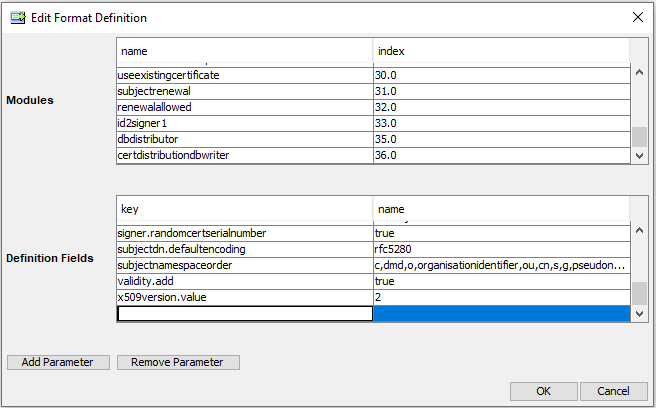
A pop-up window will appear containing all fields and modules from the selected format file.
-
The modules are shown in the top section with their indexes in the right column (the indexes determine the execution order of the modules).
-
The format definition fields are shown in the bottom section with the values of the parameters in the right column. You can edit the values for the definition fields parameters and store them for this particular procedure.
Here is an example with the certificate format rfc5280.
-
-
-
To add new format definition fields or modules click Add Parameter or Add Module. For added fields and modules (that are not present in the format file) you can edit values in the left column and also remove the row with Remove Parameter or Remove Module.
The new values will take precedence over the values in the format file, but the format file will not be affected by these changes.
-
-
Continue to set the certificate attributes.
Set certificate attributes
To set certificate attributes:
-
Select the required Country attribute.
-
Enter the Organization and Organizational Unit names.
-
In Common Name, enter a new CA name. The CA name will appear in the CA certificate.
For customizing the attribute display, see step 4. Also, if Subject Information Access attribute is chosen, see step 5.
-
If you want to change what certificate attributes to be displayed, do the following:
-
Click Browse, to the right of the certificate attributes.
-
Select which attributes to present and click OK.
The attributes will be shown in the same order as they are listed in this dialog box.The Auto add data fields option is used to present all available fields of an existing certificate. It is not applicable in the Create CA Request dialog.
-
-
If Subject Information Access is displayed, do the following:
For information concerning the subject information access extension, refer to RFC 5280 - Internet X.509 Public Key Infrastructure Certificate and CRL Profile.
-
Click the + button associated with the Subject Information Access field to open the fields below.
-
Enter the Access method OID to be used.
-
Select either the URI or E-mail option button in the Access Location section and enter the required information.
-
Click Finish.
-
Click OK to close the dialog.
-
-
In Create Authority Request, click OK. The Signature dialog box appears. See Sign tasks in Certificate Manager for more information.
Additional information
