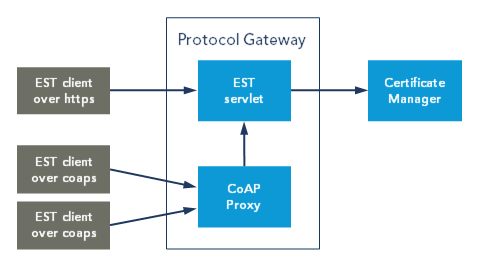
This article describes the support for the Enrollment over Secure Transport (EST) protocol in Nexus Certificate Manager via Protocol Gateway.
The Enrollment over Secure Transport (EST) is a cryptographic protocol that describes an X.509 certificate management protocol targeting Public Key Infrastructure (PKI) clients that need to acquire key pairs, client certificates and associated Certification Authority (CA) certificates over https. Example of functions are initial certificate enrollment, certificate renewal, and CA rollover. EST is defined in RFC 7030. See also Example: EST configuration in Protocol Gateway.
EST endpoints
The EST service is compliant with the EST specification and supports the following endpoints:
|
endpoint |
Operation |
|---|---|
|
/cacerts |
CA Certificates request and response |
|
/simpleenroll |
Simple enrollment and re-enrollment of Clients with response |
|
/simplereenroll |
Simple enrollment and re-enrollment of Clients with response |
|
/fullcmc |
Full Certificate Management over CMS (CMC) request and response |
|
/csrattrs |
Server-side key generation request and response with symmetric and asymmetric private key encryption |
|
/serverkeygen |
Certificate Signing Request (CSR) attributes request and response |
For more information on client authentication and preregistration, see Authentication and preregistration for EST.
For details on the EST protocol, see https://tools.ietf.org/html/rfc7030.
The default configuration for EST and the CoAP proxy is included in est.properties and coap.properties.
CoAP Proxy
EST over secure CoAP (EST-coaps) is a protocol that can be used for secure bootstrapping and certificate enrollment to low-resource devices. Constrained devices can be battery powered and unattended for years, supporting DTLS, 6LoWPAN; IPv6 over IEEE 802.15.4 based networks. Contiki NG OS based devices is an example of clients that can use EST over coaps.
In Protocol Gateway, there is a CoAP Proxy bundled with the EST service, to allow constrained devices to request certificates over CoAP instead of HTTP. This proxy is powered by the open-source Eclipse project Californium and can be enabled and configured in coap.properties. For general information on EST over CoAPs, see Internet draft - EST over secure CoAP (EST-coaps).
The CoAP proxy consumes CoAP(s) requests and forwards them as HTTP requests to the EST service using TLS client authentication with the officer configured in cm-gateway.properties. For more information, see Initial configuration of Protocol Gateway. The original client certificate is forwarded as well, to ensure that the client is authorized for reenrollment.
The CoAP proxy does not support /fullcmc.
The CoAP proxy fetches all open CA certificates from CM at startup and uses them as its truststore. In the current implementation there is a limitation that the CoAP proxy does not allow multiple CA certificates to have the same subject.
The Datagram Transport Layer Security (DTLS) server certificate, that is needed for CoAPs and configured with the parameter tlsToken, must include the extended key usage Server Authentication.
Related information
