This article is new for Identity Manager 6.0.
This article describes how to do remote ID verification using OpenID Connect (OIDC) service tasks with E-Ident or another OpenID Connect provider. For more details about the service tasks, see “OpenID Connect: Authorization request service task“ and “OpenID Connect: Verify JWT claims service task“ in Miscellaneous standard service tasks in Identity Manager.
Prerequisites
-
Identity Manager version 6.0.
-
An account with the E-Ident service or another OpenID Connect provider.
Overview
The implementation supports:
-
Creating an OIDC Authorization Code request
-
Handling the OIDC callback
-
Storing validated ID token claims in the process
-
Optionally verifying selected JSON Web Token (JWT) claims against internal process data
The remote ID verification process is based on two steps:
-
The OIDC: Authorization request service task starts the authentication flow. See Miscellaneous standard service tasks in Identity Manager for details.
-
The OIDC: Verify JWT claims service task validates the identity data returned after successful authentication. See Miscellaneous standard service tasks in Identity Manager for details.
Together, these tasks form the foundation of the remote ID verification process.
Authorization code flow
The implementation uses the Authorization Code flow as described in the E-Ident Open ID Connect documentation.
At a high level, the flow is:
-
BPMN service task creates the OIDC authorization request.
-
The authorization request is stored in the process map.
-
The user is redirected to the OIDC provider.
-
The provider calls the Smart ID Identity Manager callback.
-
The callback exchanges the authorization code for tokens.
-
The returned ID token is decoded and validated.
-
On success, the validated JWT claims are stored in the process map.
-
A second optional service task can verify selected JWT claims against internal values.
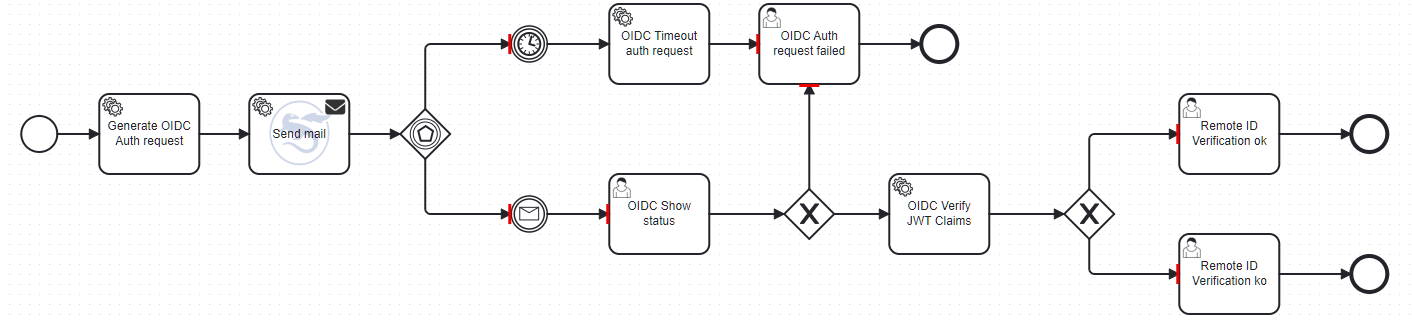
Process example
Here is a process example about doing a Remote ID verification by email:
Identity Provider configuration
Identity Manager Operator exposes a callback endpoint to handle the OpenID Connect authorization code flow.
This endpoint must be registered as a redirect URI in your Identity Provider configuration: /ws/oidc/callback
Example:
https://idm.smartid.example.com/ws/oidc/callback
