This article is valid for Smart ID 21.10 and later and Digital Access 6.1.0 and later.
This article describes the SAML Single Logout feature in the Smart ID Digital Access component.
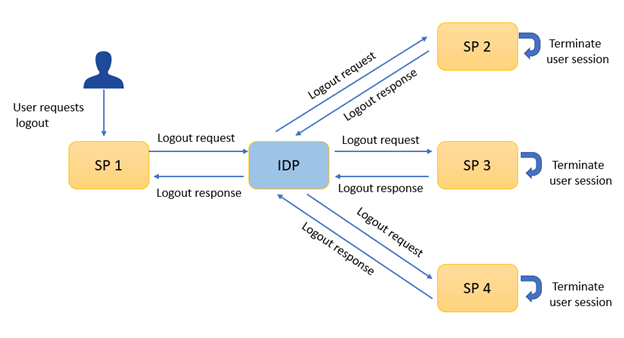
SAML Single Logout (SLO) is a SAML flow that allows the end-user to log out from a single session and be automatically logged out of all related sessions that were established during Single Sign-On (SSO).
The end-user can initiate the SLO process from within the Identity Provider (IDP) or one of the Service Providers (SPs). Currently only the front channel SLO works with http-redirect.
Enable Single Logout when Digital Access acts as IDP
IDP initiated logout flow
SP initiated logout flow
Other